Zama (ZAMA): Enabling confidential computing on-chain with FHE
Public blockchains have a fundamental transparency problem — their open verification model makes them unsuitable for handling sensitive data, such as financial assets or personal identity. The Zama (ZAMA) open-source project addresses this limitation through its Confidential Blockchain Protocol, which adds a programmable privacy layer to web3. The protocol uses Fully Homomorphic Encryption (FHE) to enable confidential smart contracts that run computations on encrypted data without ever exposing the underlying values to validators or the public. Transaction inputs and states stay private, while the network still verifies everything publicly.
Developers can build confidential applications through Zama’s FHEVM, a Solidity library that brings encrypted data types into standard smart contract development. Behind the scenes, a multi-party computation (MPC) key management service (KMS) manages cryptographic keys, and zero-knowledge (ZK) proofs validate user inputs before processing. This lets Zama support composable, confidential apps on existing Layer 1 and Layer 2 chains without touching their networks’ trustless validation mechanisms.
Key Takeaways:
Zama (ZAMA) is a modular confidentiality layer for blockchains that enables confidential computing and smart contracts by leveraging FHE encryption technology.
Zama's privacy layer features a high degree of cross-chain compatibility, and can be integrated into any Layer 1 or Layer 2 network.
The platform's native cryptocurrency, ZAMA, is primarily used for staking and to pay the protocol fees for the use of encrypted computational resources.
What is Zama?
Zama (ZAMA) is an open-source cryptography company whose core mission is to build a modular confidentiality layer for the global blockchain ecosystem. Rather than launching a competing standalone chain, the Zama protocol operates privacy infrastructure that integrates directly into existing decentralized networks.
By addressing the inherent lack of privacy on public blockchains, the company aims to transition web3 from a state of total transparency to one where sensitive data is protected by default.
The confidentiality layer for blockchains provided by Zama leverages FHE, a cryptographic method that enables computations over fully encrypted data. Through its flagship tools, such as the FHEVM and TFHE-rs Rust libraries, Zama empowers the development of "blind" smart contracts.
These confidential smart contracts possess the unique ability to process and transform data even as it remains entirely encrypted. This means that the contract logic can execute functions, such as adding balances or verifying identities, without node operators on the network or the public ever seeing the underlying values. Such methodology preserves the integrity and verifiability of the blockchain while ensuring data confidentiality during the computation process.
This architecture combines FHE for encrypted computation, MPC for decentralized key management and lightweight ZK proofs for input validation — forming a scalable and publicly verifiable confidentiality stack.
Functioning as a universal privacy layer, Zama's protocol is designed for broad compatibility. It can be integrated into any Layer 1 or Layer 2 network, including popular smart contract chains like Ethereum (ETH) and Solana (SOL). This allows developers to add confidential features to their existing tech stacks without requiring users to migrate to a new chain.
What is Fully Homomorphic Encryption (FHE)?
FHE is a cryptographic technique that allows you to run computations on encrypted data without ever needing to decrypt it. In traditional cryptography, data must be converted to plaintext in order to be processed, which is a significant security risk because the server or node performing the work can see everything. This creates a clear vulnerability because transaction data is exposed the moment it’s used.
With FHE, data stays encrypted throughout the entire execution of a function. The output is an encrypted value that only the intended recipient can actually read. This keeps data private throughout the life cycle of a transaction, and the entity performing the calculation never sees the actual values that it’s manipulating.
This capability is what makes end-to-end confidentiality possible. Most encryption methods only protect data while it's sitting on a drive or moving across a network, but they can fail when the data is actively being processed on the network.
FHE ensures that data is never exposed during computation. This means that validators can process transactions without ever seeing the private data they contain. The protocol remains verifiable because anyone can rerun the operations on the encrypted data to confirm the results are valid, without needing the raw plaintext.
FHE is often compared to another privacy-preserving technique: ZK proofs. However, these two techniques serve different purposes. ZK technology is great for proving that a statement is valid without revealing the data behind it, while FHE is designed to actually compute and change that hidden data. These two technologies may be used as complementary tools, rather than as mutually exclusive alternatives.
At the same time, FHE’s ability to handle complex calculations on encrypted data makes it the right fit for confidential smart contracts in which multiple parties interact with private data.
How does Zama work?
Zama functions as a modular confidentiality layer designed to integrate with existing blockchain networks, such as Ethereum or Solana. This architecture avoids the need for dedicated private networks, and supports full composability and confidential smart contracts that interact with public ones in the same environment.
The primary framework for this is FHEVM, a library that enables developers to write confidential contracts using standard Solidity programming language. It introduces encrypted data types that allow contract logic to process values while they remain private, ensuring that network nodes never access the underlying data. This approach enables developers to maintain the security of public ledgers while handling sensitive information, such as account balances, identities and private voting tallies.
Zama’s technical foundation relies on the TFHE-rs and Concrete libraries. TFHE-rs is a high-performance Rust library that implements the core FHE operations, providing the necessary primitives for encrypted computation. Meanwhile, Concrete is a compiler that translates standard code into FHE-ready instructions. This compiler automates complex cryptographic tasks and allows developers to implement private logic without manual cryptographic configuration.
These tools ensure that encrypted operations maintain the same functional accuracy as traditional plaintext computations, thereby removing the barrier to entry for developers who aren’t specialized in advanced cryptography.
Processing Zama transactions involves a hybrid model that utilizes coprocessors and a key management service (KMS). Because FHE is computationally intensive, execution is offloaded to specialized off-chain coprocessors that return the results to the host chain, maintaining network scalability. Security is managed by a decentralized KMS using multi-party computation (MPC). The decryption key is fragmented among multiple nodes, and requires a specific threshold majority to authorize any decryption or verification. This distribution ensures that no single entity can access private transactional data.
What is the ZAMA crypto token?
Zama's native crypto token, ZAMA, has two primary functions — payment for protocol fees, and staking.
The token is used to pay protocol fees (referred to as private gas), though these aren’t standard gas fees. Rather, they specifically cover the cryptographic cost of verifying encrypted inputs, performing FHE computations and managing decryptions. These fees are priced in USD but are paid in ZAMA tokens. Critically, 100% of these fees are burned by the protocol, thereby creating a direct relationship between network usage and token value.
The ZAMA token is also used for staking to secure the Zama network’s infrastructure. Operators of FHE coprocessors and KMS nodes must stake ZAMA to participate in the network and earn rewards. These rewards are paid through new token emissions, initially set at 5% annually.
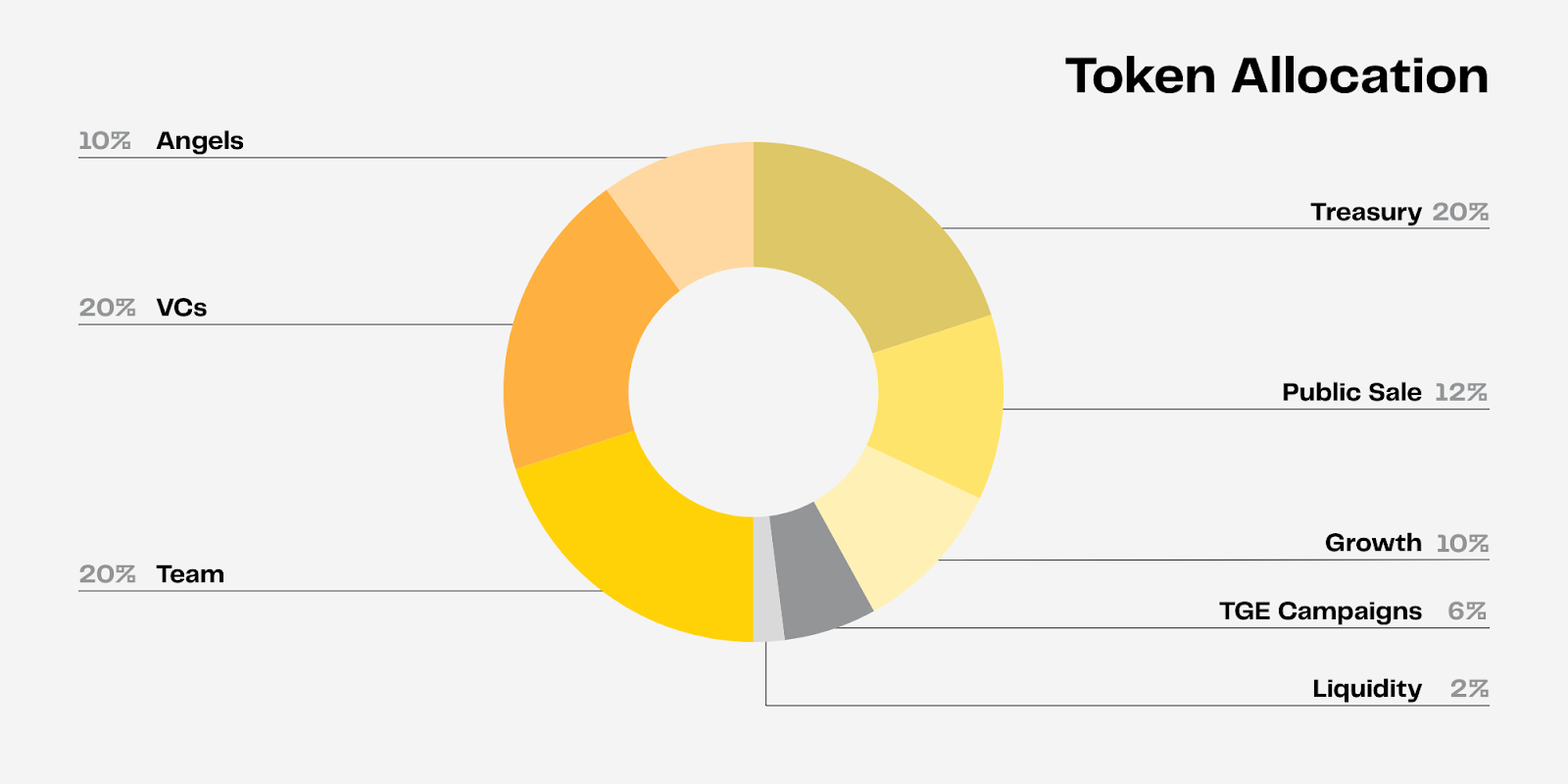
ZAMA is an Ethereum-based ERC-20 asset with a total supply of 11 billion. The token's supply allocation shares are shown in the chart below.
Zama Protocol real-world applications
Potential applications of Zama's confidential blockchain protocol span multiple sectors for which confidentiality is a prerequisite for professional or institutional adoption. In the financial sector, the protocol enables confidential payments for stablecoins and payroll systems. By keeping balances and transfer amounts encrypted end-to-end, users can settle transactions on public ledgers such as Ethereum without exposing their financial details.
This capability also extends to the tokenization of real-world assets (RWAs). Traditional institutions often avoid public chains, due to confidentiality and compliance risks. However, Zama enables the tokenization of stocks, bonds and derivatives while keeping investor identities and transaction history private.
Within decentralized finance (DeFi), Zama's technology may help address the issues of public exposure and predatory bot activity. Encrypted swaps prevent front-running by hiding transaction details from the mempool until they’re processed. At the same time, confidential lending and on-chain credit scoring allow participants to prove creditworthiness without revealing the entire contents of their portfolios.
Additional benefits of FHE
FHE may also help reduce front-running on decentralized exchanges (DEXs) by keeping trade details encrypted until execution. By preventing transaction intent from being exposed in advance, it can improve execution fairness and reduce the risk of exploitation via bots.
Identity and governance also benefit from Zama’s encrypted data tools. Users can manage decentralized identities and customer data on-chain, where sensitive personal data remains encrypted yet fully functional for interacting with other applications. This concept of identity abstraction allows private compliance checks, whereby a smart contract can verify a claim, such as being over a certain age, without seeing the user's birth certificate.
Within decentralized governance, FHE enables private voting on decentralized autonomous organizations (DAOs) and organizational blockchains. Votes and individual stake weights are kept hidden, ensuring that only the final tally is revealed, in order to prevent bribery, blackmail or social pressure.
Beyond these core areas, Zama enables the operation of on-chain corporations, so that cap tables and financials stay private while still being automated by smart contracts.
The technology also supports data marketplaces for AI. In these marketplaces, users can sell data for model training while keeping the source data encrypted, ensuring they retain ownership while they participate in the digital economy.
Another potential area for the application of Zama's technology is in on-chain forecasting platforms. These markets are often distorted when newer predictions are affected by earlier participants. When using Zama, these platforms can preserve the confidentiality of past predictions by revealing them at specific regular intervals, thus improving the reliability of the overall integrity of the forecasting process.
Where to buy the ZAMA crypto token
The ZAMA token is available on Bybit as a Spot pair with Tether (USDT) and as a USDT-based Perpetual contract. It’s also available on the Bybit Alpha platform, which lets you trade on-chain directly via your Bybit Unified Trading Account (UTA), without any need to manage gas fee tokens or blockchain wallets. By leveraging your UTA for all on-chain operations, you can take advantage of decentralized trading opportunities, even if you’re not intimately familiar with DeFi or blockchain networks.
Conclusion
By pioneering a cross-chain confidentiality layer, Zama makes programmable confidentiality easily available to web3 developers. This creates tremendous potential to move blockchain applications from niche use cases to mainstream enterprise adoption. A large spectrum of opportunities are emerging, thanks to Zama's confidential computing model based on FHE. These include confidential finance, RWAs, on-chain governance, identity solutions and AI marketplaces — to name just a few.
The Zama protocol isn’t just providing a confidentiality-protecting blockchain layer — it’s paving the way for the future "confidentiality-first" internet we’ve so often heard about.
#LearnWithBybit